March’s Patch Tuesday release continues a streak of zero-days fixed by Microsoft that has lasted since June 2022. Two actively-exploited zero-day vulnerabilities were fixed this month, one in the near-ubiquitous Outlook application that allows attackers to spoof after stealing a user’s Net-NTLMv2 hash. The other is yet another security feature bypass in Windows SmartScreen.
On the whole, this month’s Patch Tuesday sees a total of 85 vulnerabilities patched, 9 of which are critical, and the two zero-days listed above. Of the critical vulnerabilities yet to be exploited, administrators should prioritize a critical, CVSSv3.1 9.8/10 remote code execution vulnerability affecting most Windows operating systems in the Internet Control Message Protocol (ICMP).
In case you’re unfamiliar, remote code execution (RCE) is an attack where the attacker can access the device and execute malicious code. The impact of remote code execution can make the attacker gain complete control over the compromised machine.
There’s also a critical vulnerability in Windows Cryptographic Services affecting Windows 10, 11, and Server 2012 forward that allows for arbitrary code execution if an attacker can install or coerce the victim to install a malicious certificate on their device.
Microsoft Patch Tuesday Vulnerabilities: A Brief History
CVE-2023-23397 – Microsoft Outlook Elevation of Privilege Vulnerability [CRITICAL ZERO-DAY]
CVE-20223-23397 is an actively exploited zero-day vulnerability in Microsoft Outlook that allows attackers to obtain users’ Net-NTLMv2 hash and utilize the hash in an NTLM relay attack against another service, authenticated as the victim - otherwise known as spoofing.
The vulnerability scores a 9.8/10 CVSSv3.1 and can be exploited via email, potentially when the message is retrieved and processed by the server, meaning that exploitation could occur before the email is viewed by a user with the Preview Pane. Both 32 and 64-bit versions of Microsoft 365 Apps for Enterprise, Office 2013, 2016, and 2019 (as well as LTSC) are vulnerable to attack.
Administrators should patch within the day if possible since the vulnerability is relatively simple to exploit, doesn’t require user interaction, and is already being exploited in the wild. Microsoft has shared two temporary mitigations if you’re unable to patch immediately, both of which will impact NTLM and applications that use it so proceed with caution. The first option is adding users to the Protected User Security group which will prevent the use of NTLM as an authentication method, using this approach for high-value accounts like Domain administrators may be a reasonable approach. The other mitigation is to block TCP 445/SMB outbound on your firewall which will prevent sending NTLM authentication to remote fileshares. – Peter Pflaster
CVE-2023-24880 – Windows SmartScreen Security Feature Bypass Vulnerability [IMPORTANT ZERO-DAY]
CVE-2023-24880 is an actively exploited zero-day vulnerability affecting all Windows desktops (Windows 10 and above) and server editions (Server 2016, 2019, and 2022).
Microsoft Mark of the Web (MOTW) is a built-in Windows security feature that stops users from downloading or accessing malicious files from the internet by creating a zone identifier Alternate Data Stream (ADS), which enables Windows SmartScreen to block access to security features on the devices. However, the attacker can craft a malicious file bypassing the MOTW, resulting in a loss of device integrity and availability of security features in Microsoft office, such as Protected view, which relies on MOTW tags.
Automox recommends patching this vulnerability within the day (if possible) since the vulnerability is actively exploited in the wild to minimize exposure to unnecessary cyber risks. – Preetham Gurram
CVE-2023-23415 – Internet Control Message Protocol (ICMP) Remote Code Execution Vulnerability [CRITICAL]
CVE-2023-23415 is a new network remote code execution vulnerability targeting Internet Control Message Protocols, or ICMP. Often used for error reporting, ICMP is a network layer protocol employed by network devices to diagnose communication issues by validating that data has reached its intended destination promptly.
An attacker can remotely exploit this vulnerability through the use of a low-level protocol error containing a fragmented IP packet in its header that is sent to the target machine. To trigger the vulnerable code path, an application on the target must be bound to a raw socket which allows for direct access to the IP. This vulnerability impacts a wide range of Microsoft products, including Windows 10, Windows 11 as well as Windows Server 2008, 2012, 2016, 2019, and 2022.
With low attack complexity, and minimal requirements for an attacker to be successful (no user interaction or privileges required), Automox encourages users to patch asap with the official fix already released by Microsoft. – Gina Geisel
CVE-2023-23416 – Windows Cryptographic Services Remote Code Execution Vulnerability [CRITICAL]
CVE-2023-23416 is a critical vulnerability that affects all versions of Windows desktops (Windows 10 and above) and server editions (Server 2012 and above). To exploit this vulnerability, the attacker must import a malicious certificate onto the host machine. This type of exploit is also known as Arbitrary Code Execution (ACE). The attacker or victim must execute code from the local machine to exploit this vulnerability.
Automox recommends patching this vulnerability within 72 hours to minimize exposure to unnecessary cyber risks. – Preetham Gurram
Automate Patch Tuesday NOW
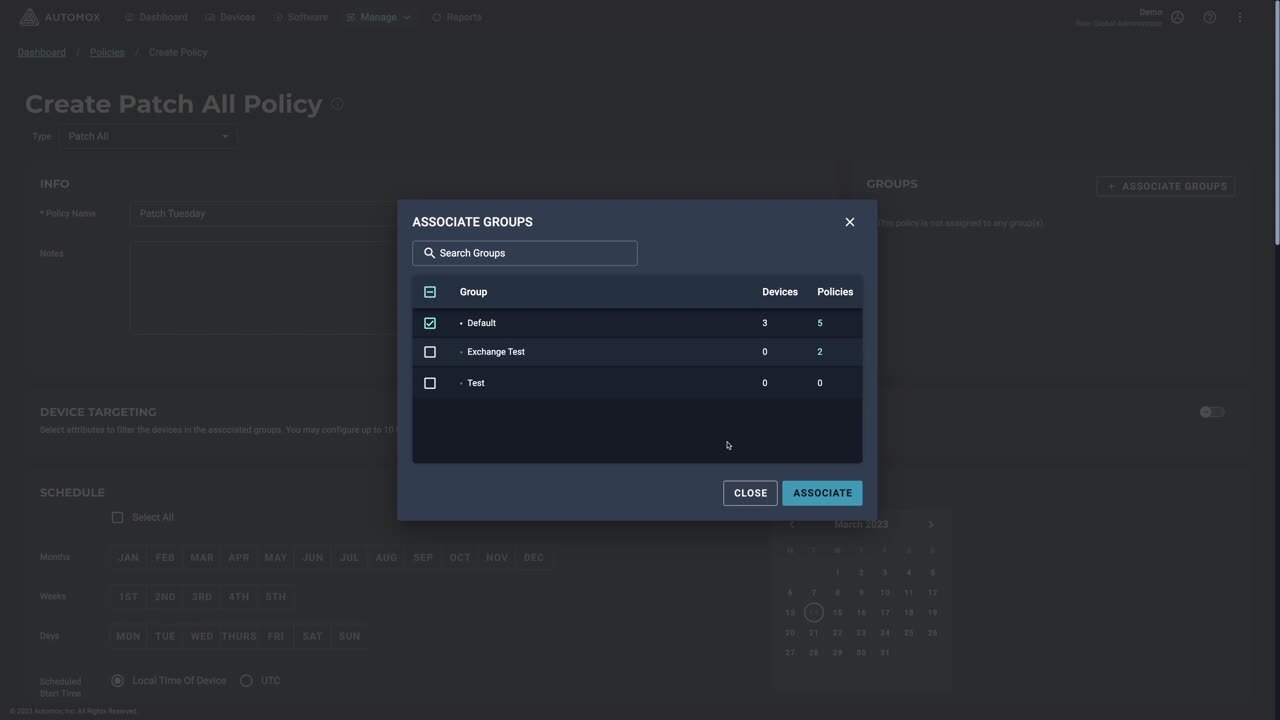
Tired of the Patch Tuesday fire drill? Automate it in 30 seconds with Automox and sleep well knowing you’re covered next month.

)

)