"We're automated." It's the standard answer from IT leadership. But dig into the daily workflows, and you find a different truth.
It is often a fragile mix of manual intervention and legacy scripting. The data from Automox's 2026 State of Endpoint Management report bears this out.
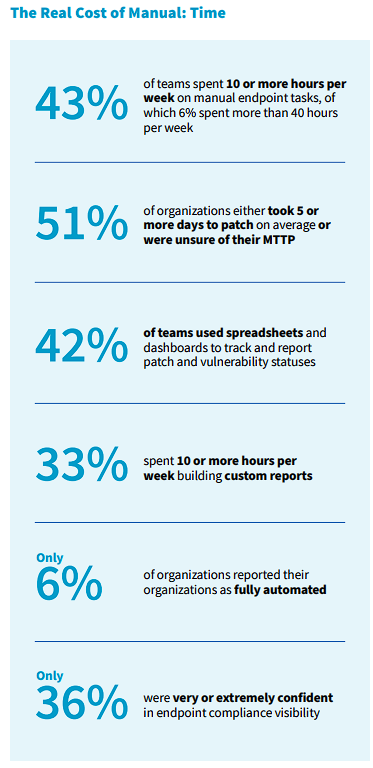
Despite the investments in tools, 43% of IT teams are still stuck spending 10+ hours a week on manual endpoint tasks.
Losing ten hours a week is more than an inconvenience. It is a direct line to risk. Partial automation creates dangerous confidence. Organizations feel covered because the easy work is handled by machines, but the highest-risk tasks still wait for a human to log in. We have effectively solved the easy problems and left the dangerous doors unlocked.
The efficiency illusion that's leaving doors open
Teams often confuse script-based task management with genuine autonomy. 57% of organizations describe their recurring task management as "partially automated via scripts or custom workflows." And just only 6% report being fully automated, creating a dangerous middle ground. It forms the illusion of speed and leaves gaps that don't show up on a quarterly efficiency report, but do show up during an incident.
Attackers don't operate based on averages but on the exceptions and the gaps. Automox Security Manager Ryan Braunstein believes this operational lag is a direct threat vector. "Manual work is the new attack surface," Braunstein said. "Every manual task, whether it's managing tickets, tracking spreadsheets, or manually patching systems, provides extra time for an attacker to exploit something."
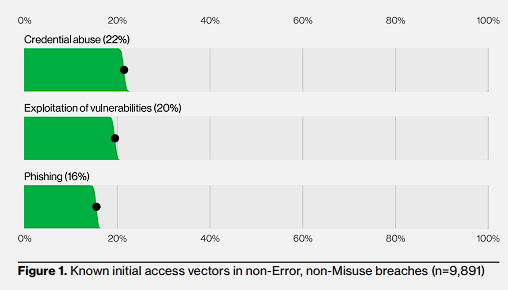
The data bears this out. Verizon's 2025 Data Breach Investigations Report (DBIR) shows vulnerability exploitation was the entry point for 20% of breaches. SANS Institute and CrashPlan data is just as concerning: 55% of organizations still have PII on endpoints, regardless of internal policies. The tools are there, but the enforcement isn't. Partial automation cuts down the manual steps, but it fails to actually close the loop on risk.
Visibility gaps are where risk accumulates
Security doesn't happen in a spreadsheet. Yet the Automox 2026 State of Endpoint Management report found that 42% of teams still rely on them or fragmented dashboards to track vulnerabilities. Only 17% have a truly unified view. The real issue here is latency. Making decisions on three-day-old data is structurally dangerous. The risk profile changes by the minute, even if your spreadsheet doesn't.
The industry is moving too fast for manual reconciliation of data. CrowdStrike's 2025 data shows the average eCrime breakout time, the time it takes an intruder to move laterally after initial compromise, has plummeted to just 48 minutes. Compare that asymmetry to Verizon DBIR's finding, which places the median remediation time for edge device flaws at 32 days.
Adaptiva's research further highlights the operational drag. It notes that 77% of organizations need a week or longer just to deploy patches. When visibility is fractured across multiple dashboards, IT leaders are forced to make security decisions based on stale intelligence. In a 48-minute breakout window, a week-long patch cycle isn't a defense strategy; it's a liability.
What partial automation actually looks like at scale
To understand the failure of partial automation, you have to look at what's actually being automated. The Automox report shows that 50% of organizations automate OS patching and 46% automate endpoint inventorying. While helpful, these are only siloed wins. A patched OS doesn't protect against a vulnerable third-party application if the deployment process for that app remains manual.
The data reveals that 37% of teams still rely on manual procedures for recurring tasks, and 33% spend over 10 hours weekly just building custom reports to make sense of their environment. This suggests that organizations have automated the "action" but not the "intelligence" or the "verification."
This accumulation of ad hoc scripts and one-off configurations creates automation debt. It functions like technical debt: it appears to work today but becomes increasingly fragile and difficult to maintain over time.
IDC reports that 47% of CIOs who expect to overspend on digital infrastructure blame excessive tech debt. This isn't just a security problem; it's a business sustainability problem where teams eventually spend more time maintaining their "automation" than actually securing the network.
The blockers are known. The cost of waiting is growing.
Budget constraints, legacy systems, and skills gaps all pose consistent barriers to closing these gaps.
Budget, legacy tech, and skills gaps were each cited by roughly a third of respondents. But with the average global breach costs at $4.44 million, and over $10 million in the US, the "insufficient budget" excuse collapses.
Leaders who view these blockers as immovable are gambling. They are betting manual work can outrun automated attacks, a strategy that is statistically failing.
The automation gap doesn't close itself
The "good enough" era of patching is over. Fragmented visibility leaves exposure windows that modern attackers will find.
While budget and technical debt are real barriers, the financial risk of inaction is far higher. For 2026, MTTP and MTTR must become board-level KPIs.
The technology for autonomous management is here. The only question is whether teams will close the loop now or wait until an adversary does it for them.
Sources
Automox 2026 State of Endpoint Management Report - All Automox survey data (43% manual hours, 57% partial automation, 42% spreadsheets, 6% fully automated, 50% OS patching, 46% endpoint inventorying)
Verizon 2025 Data Breach Investigations Report - 20% of breaches via vulnerability exploitation, 32-day median remediation time
SANS Institute / CrashPlan Endpoint Data Survey - 55% of organizations have PII on endpoints
CrowdStrike 2025 Global Threat Report - 48-minute average eCrime breakout time
Adaptiva 2025 Patch Management Report - 77% of organizations need a week or more to deploy patches
IBM Cost of a Data Breach Report - $4.44 million average global breach cost
CIO / IDC Tech Debt Survey - 47% of CIOs blame excessive tech debt for overspending
Frequently asked questions
According to the Automox 2026 State of Endpoint Management report, 43% of IT teams spend 10+ hours per week on manual endpoint tasks, and only 6% report being fully automated.
Partial automation creates a false sense of coverage. Teams automate routine tasks like OS patching, but leave higher-risk activities like third-party app deployment and vulnerability verification as manual processes. Attackers exploit these gaps, not the automated portions.
CrowdStrike's 2025 data shows the average eCrime breakout time has dropped to just 48 minutes, meaning attackers can move laterally within an organization before most teams can even identify the breach.
Automation debt is the accumulation of ad hoc scripts, one-off configurations, and fragmented workflows that appear to work but become increasingly fragile over time. Like technical debt, it compounds and eventually costs more to maintain than to replace with a unified solution.
Adaptiva's research shows that 77% of organizations need a week or longer to deploy patches, while the Verizon DBIR places median remediation time for edge device flaws at 32 days. This delay creates significant exposure windows.

)
)
)
)