We are looking at a math problem that no longer balances.
On one side, CrowdStrike's 2025 Global Threat Report pegs the average eCrime breakout time at 48 minutes, with the fastest intrusion clocking in at 51 seconds. On the other side, the 2025 Verizon DBIR shows edge device remediation dragging out to a median of 32 days.
That disconnect represents the biggest liability in cybersecurity today. Exposure time has graduated from an operational KPI to a defining security metric.
As long as we rely on humans to bridge the gap between 48 minutes and 32 days, we will fail. Autonomous endpoint management isn't about saving time, it's about matching the adversary's speed.
The exposure window is the attack surface
Traditional patching windows are dead as weaponization is happening too fast. Within 24 hours of disclosure, 33% of critical vulnerabilities see active exploitation. Within a week, that number hits 54%. The sheer volume of threats makes this velocity even more dangerous.
The CISA Known Exploited Vulnerabilities catalog added 132 new CVEs in just 2025's first half (a 80% YoY jump). Indusface backed this up with a 124% surge in vulnerability-based attacks in Q3 2024.
For teams stuck on manual processes, this isn't a backlog. It is an impossible race. Every minute a system remains unpatched after disclosure constitutes a measurable risk. Automox Security Manager Ryan Braunstein frames this operational lag as a direct vulnerability to organizations.
"Manual work is the new attack surface. Every manual task, whether it's managing tickets, tracking spreadsheets, or manually patching systems—provides extra time for an attacker to exploit something," he said.
Braunstein's observation reflects a hard truth: attackers capitalize on the latency built into human-driven workflows.
What MTTP really measures
Mean Time to Patch is often treated as an IT performance metric. But it actually measures how much risk an organization is willing to carry in today's threat environment.
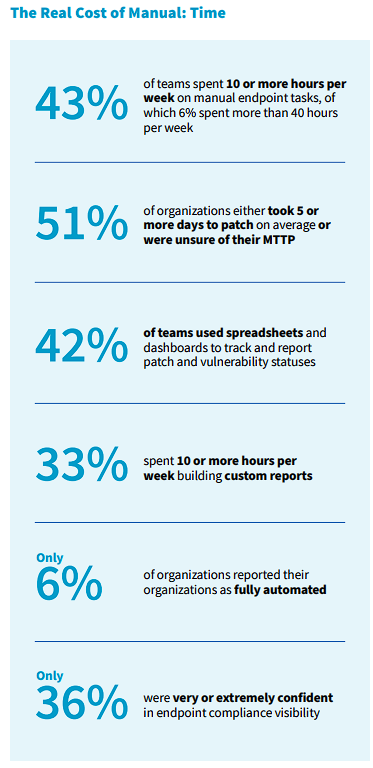
The Automox 2026 State of Endpoint Management report reveals a concerning baseline: 51% of organizations either take five or more days to patch on average or are unsure of their MTTP entirely. Only 1 in 10 organizations reports an MTTP of less than a day.
This lag persists even though the NIST SP 800-40 guidance's recommendation for critical security patches to be installed within 30 days. Even that conservative federal benchmark is being missed by more than 52% of enterprises.
These delays have severe consequences: IBM 2025 data shows it took an average of 204 days to discover a breach and an additional 73 days to contain it. When organizations cannot answer "what is our mean time to patch" with precision, they are effectively flying blind regarding their real-time risk posture.
MTTP is no longer just about compliance; it measures the duration an organization remains open to compromise.
Why partial automation doesn't solve the exposure problem
Periodic scanning and human-approved patching, partial automation, doesn't solve the exposure problem. Standard intervals and approval processes bake latency into the system. Nor does it fix the workload issue.
Adaptiva data shows 98% of IT pros find patch deployment disruptive to their other duties. Even with some automation, that friction causes teams to delay updates, widening the exposure window.
The market is already adjusting to this reality. Gartner projects that 75% of legacy detection technologies will integrate preemptive defense by 2030. This means that we are moving toward autonomy because we have to.
The guardrail problem and why it's solvable
Engineers are right to be skeptical of full autonomy. The concerns about control are valid. The Automox report backs this up: 46% of respondents worry about data privacy, 44% fear unauthorized changes, and 36% simply don't trust AI recommendations yet.
But these are engineering problems, and they have solutions. The report shows exactly what builds trust: automatic rollbacks (43%), pause buttons (42%), and solid audit logs (42%).
Put those guardrails in place, and the hesitation fades. Autonomous systems offer consistency manual work can't match, as long as the oversight is real.
The metric that should define your security posture in 2026
Vulnerability exposure time is now the most operationally consequential security metric an organization can track. Attacker breakout times are measured in minutes, while defender response times often stretch into weeks. Autonomous endpoint management is currently the only mechanism capable of compressing remediation timelines to match the speed of the adversary.
The financial and operational incentives for closing this gap are clear. IBM found that organizations using AI-powered systems detected and contained breaches 108 days faster and saved an average of $1.76 million per breach.
With the guardrails for autonomous systems now well-understood and accessible, the hesitation to automate is becoming a liability. Framing autonomous endpoint management merely as an efficiency tool misses the larger picture. In 2026, autonomy is a fundamental risk management imperative.
Sources
Originally published on Hackread - Original article
CrowdStrike 2025 Global Threat Report - 48-minute average eCrime breakout time, fastest intrusion at 51 seconds
Verizon 2025 Data Breach Investigations Report - 32-day median edge device remediation time
Automox 2026 State of Endpoint Management Report - 51% take 5+ days to patch, 46% worry about data privacy, 44% fear unauthorized changes, trust-building guardrails data
CISA Known Exploited Vulnerabilities Catalog - 132 new CVEs in first half of 2025, 80% YoY increase
Indusface Cybersecurity Statistics - 124% surge in vulnerability-based attacks in Q3 2024
NIST SP 800-40 Rev. 4 - Federal patch installation guidance (30-day benchmark)
IBM Cost of a Data Breach Report - 204-day average breach discovery, 73-day containment, $1.76M savings with AI-powered systems
Adaptiva 2025 Patch Management Report - 98% of IT pros find patch deployment disruptive
Gartner Preemptive Defense Forecast - 75% of legacy detection technologies to integrate preemptive defense by 2030
Frequently asked questions
eCrime breakout time is the duration it takes an attacker to move laterally after initial compromise. CrowdStrike's 2025 data places the average at 48 minutes, with the fastest at just 51 seconds. This matters because most organizations take days or weeks to patch, meaning attackers can move freely long before defenses respond.
MTTP measures the average time between a patch being available and it being deployed. According to the Automox 2026 State of Endpoint Management report, 51% of organizations take five or more days to patch or don't know their MTTP at all. This metric directly reflects how long an organization remains exposed to known vulnerabilities.
Partial automation still relies on human approval cycles and scheduled scanning intervals, which bake latency into the process. Adaptiva data shows 98% of IT pros find patch deployment disruptive even with some automation in place. The exposure window remains open because the process still depends on manual steps at critical points.
The Automox report identifies three features that build trust in autonomous systems: automatic rollbacks (cited by 43% of respondents), pause buttons (42%), and audit logs (42%). These controls give IT teams the ability to maintain oversight while allowing systems to operate at machine speed.
IBM data shows organizations using AI-powered security systems detected and contained breaches 108 days faster and saved an average of $1.76 million per breach compared to those without. The average global breach cost sits at $4.44 million, making the financial case for automation significant.

)
)
)
)